Preview of the full roadmap below — for the high-resolution version click here:
TLDR
- Nobody knows everything.
- Various materials are available on each topic — find what suits you best.
- The learning process may differ between people.
- There's a shortcut roadmap (red sections) to start practical hacking sooner.
- This may take years — don't rush.
- Practice makes perfect.
Tier 0 — Passion & Time
You should pick hacking because you love it, not because you want a salary. Plan to spend serious daily time reading and practising — the field grows faster than you can keep up with.
Tier 1 — Prerequisites
Networking and Protocols. If you have no networking background, work through Network+ basics. Learn the HTTP protocol deeply — recommended: HTTP: The Definitive Guide.
Programming Language. Pick Python or Go. For Python: 30 Days Of Python. For Go: Learning Go.
Linux and Bash. Linux in Action for the file system, Introduction To Bash Scripting for automation.
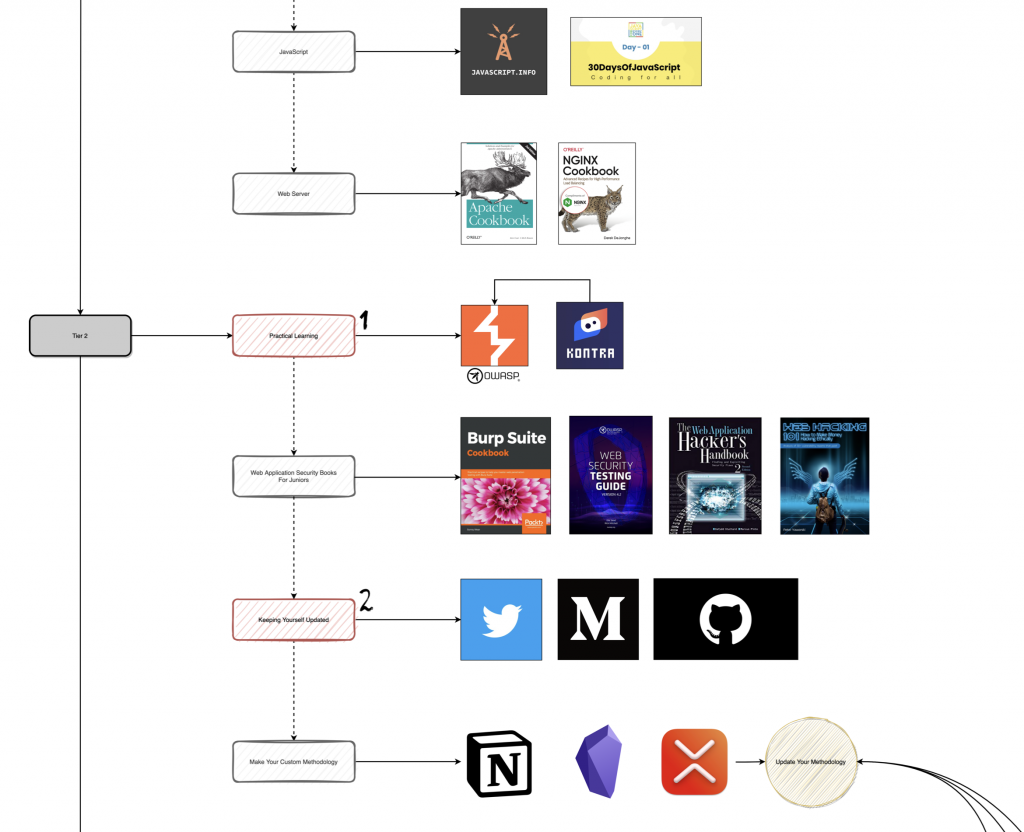
JavaScript. 30 Days Of Javascript + javascript.info.
Web Server. Apache (Apache Cookbook) and Nginx for proxies/load balancing (Nginx Cookbook).
Tier 2 — Practical Learning
Start with the OWASP Top 10. The best practical track is PortSwigger's Academy with hands-on labs. Get Burp Suite set up early — and if you want a written reference, the Burp Suite Cookbook.
Follow up with the Kontra Application Security Platform labs — both Web and API Top-10. Then circle back to PortSwigger for everything outside the Top-10.
Books for juniors:
- OWASP Web Security Testing Guide
- The Web Application Hacker's Handbook 2 — must-read.
- Web Hacking 101 — bug-hunter writeups.
Stay updated: hackers post on Twitter, Medium, GitHub. Build a follow-list and check it daily.
Make a custom methodology. Note things in Notion, Obsidian, or Xmind.
Tier 3 — Practice the Skills
Sharpen exploitation on CTFs: Hack The Box, RootMe, Try Hack Me. CTFs aren't just games — payloads from CTFs have shipped to real bug-bounty bounties. Two examples worth reading:
- YesWeHack quiz → Blaklis's solution → reused by Sam Curry on Apple.
- Orange Tsai's BlackHat talk Breaking Parser Logic — the Nginx off-by-slash first appeared in 2016 HCTF.
If you'd rather train on real targets, jump straight into bug bounty programs — VDPs first, since they're easier to find bugs on. Watch BlackHat, DEFCON, ZeroNights. Update your methodology as you learn.
Tier 4 — Going Deeper
Books for mediors:
Defender perspective:
Tier 5 — Finding Novel Techniques
At this stage you should be hunting novel techniques. The way to get there is depth: software architecture (e.g. Getting Started with OAuth 2.0, SPA Design and Architecture), web protocols (e.g. Learning HTTP/2, and follow research like HTTP/2: The Sequel is Always Worse by James Kettle), TLS internals (Bulletproof SSL and TLS), reverse-proxy quirks (Aleksei Tiurin's weird_proxies repo + Weird proxies/2, plus H2C Smuggling in the Wild, Web Cache Poisoning, HTTP Desync Attacks), and frameworks (build vulnerable apps yourself — Laravel, Django, Rails, ASP.NET each have their own default protections that shape the test cases).
Conclusion
Choose hacking as a passion and walk the roadmap. The five red sections in the diagram are the shortcut path you can take to start hacking as soon as possible — but plan to come back and fill the rest in.
Take care, and happy hacking.